Base CTF 2016 Pwn Challenges and Writeup ( Part V )
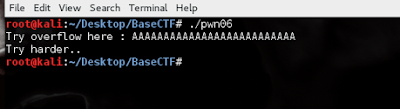
Pwn06: Try Harder!
Solution:
let begin with debugger.
Damn, he wanted “BABE” ! ;)
So, let find the crash point and combine into final payload.
Done ! :)
Enjoy guys !
Ye Yint Min Thu Htut


Comments
Post a Comment